Over 18 years ago I started working in different activities around information security like access controls, proxy, firewalls, AV, network monitoring, etc. At that time, I was reading user manuals, product documentation and lots of trial and errors to get my networks efficient and secure. However, that was very painful because at that time there were not many materials available and internet connection speeds was a shame.
When new organizations and courses started to appear life became easier. Instead of working months trying to do things the wrong way with little or bad guidance, there are now well-packaged courses that can deliver everything you need to get you started fast and point in the right direction. It is like using the right screwdriver to tighten a screw to its perfect torque and position instead of a using hammer and nail it.
I tried the offerings from many organizations, just to name a few isc2, ec-council, eLearnSecurity, CompTIA, offensive security, SANS, and all have pros and cons and will mention some of them.
My very first courses and certifications were CISSP and CEH. To me, CISSP is a great certification that serves as a glossary about information security in general and CEH serves the same purpose for penetration testing/ethical hacking. By that time I had several years already working fulltime with compliance, vulnerability assessment and remediation, and occasionally with penetration testing.
For passing the CISSP and the CEH, I read the CISSP all in one Shon Harris book and took a seminar with the Asociación Latinoamericana de Profesionales en Seguridad de Información (alapsi.net), and the official ec-council materials and the training with Código Verde (codigoverde.com), both are 40+ hour courses.
After a while eLearnSecurity appeared and have really nice courses, I had their PTP, PWD, WAPTX courses, courses are “short” (8-12hs of videos) but they include a lot of exercises and labs to do in their Hera lab and their certifications include a written exam and a self-paced 100% practical assessment to do over several days. They give very good discounts ranging from 30 to 40% during the training launch during the first few weeks only which also include a training version upgrade, current/former students receive even better discounts typically from 40 to 60%.
It was until 2014 when I give the first try to SANS/GIAC and found it to be a very good quality offer, they have lots of courses and the materials is frequently renewed but they are fairly expensive but luckily they have alternatives to have better prices for their courses and certifications.
At first, I challenged a couple of GIAC certifications without taking the associated training and succeed but had the feeling that everything was the same. It was after my first training with SANS that taking a certification turned into a way to measure my understanding on the subject.
SANS (sans.org) training catalog is huge and their sister company GIAC handles the certifications. Currently, most GIAC certifications are multiple choice exams that have to be taken in facilities approved by PearsonVUE and they are open book (you can get into the testing center and use during the exam any written material). Only the GSE which is the highest level certification which contains many requires two exams to pass, a written exam and a two-day hands-on exam. The best deal in SANS courses is through the work-study program which has only a few spots available but the discount is around 80%.
The STI, SANS Technology Institute (sans.edu) offers Master degrees and certificate programs based on SANS courses plus other subjects for master degrees, I did first their Cybersecurity Engineering Core certificate program and the followed to the Master of Science in Information Security Engineering where I am already at 23/37 credits progress. Each SANS course in the certificate program has around 25% discount and those from the master around 40% discount.
Other than the courses, I passed many other certifications (without a specific training or only reading at their study guides or because they are a subset of my daily activities) just to understand better how the vendor is evaluating the skills.
During the last few years, I had to interview several dozens of candidates for information security positions. It helps to quickly identify people base skills and that is why for me is interesting to know the contents of all those courses and certifications so when reading a CV as on the other side non-formal education or university education is so broad that makes it much more difficult to shortlist the candidates and interview only those that grabbed my attention.
Some words about the certification exams:
isc2:
- CISSP exam at that time was a written exam in paper with 100+ questions (6hs max) to evaluate the basic knowledge on ten domains and some sort of psychometric/common sense evaluation, it changed recently to adaptative exams which may be short. Very good for general infosec knowledge.
- CSSP exam is very similar to CISSP with focus on Cloud technologies, the knowledge base overlaps with the one of CISSP and it is vendor agnostic.
ec-council:
- CEH, up to version 9 was a multiple choice exam. Good as intro to penetration testing.
- CEH practical, this type of certification presents the candidate with 20 challenges to solve, pretty much like a CTF, the difficulty level is low but is definitively an improvement over written CEH exam.
AWS:
- Cloud Practitioner, is the entry level certification from AWS, the questions are pretty straight forward, it focuses on basic understanding of what services AWS offers and their names.
- Associate Architect, is a multiple choice exam, it is a must-have for anyone working with AWS to get familiar with their services.
- Security specialty, is a multiple choice exam, this cover only AWS specific stuff, it does not test the candidate security mindset. This is another must-have for people working with AWS to have the very basic security practices.
- Associate Developer, this exam may be one of the easier associate level exams, it focus in continuous integration services like CodeCommit, CodeBuild, CodePipeline.
- Associate SysOpes Administrator, the exam focuses strongly on EC2, the difficulty level is lower than the Associate Architect exam.
- Professional Solutions Architect, this is one of the most challenging AWS exams to succeed you need a solid foundations and understanding of the AWS core services and some questions and answers are crazy long so expect to have several items that will scroll over one page long so if allowed ask for the ESL facility (English as Second Language gives you 30 extra min).
eLearnSecurity:
- eCPPT, a nice intro to penetration testing, the exam is a pentest, material is a bit short but there are many labs. eLearnSecurity was acquired by INE so look for INE 1yr plans that gets you access to all eLearnSecurity and Pentester Academy trainings.
CompTIA:
- Security+, this exam covers a broad variety of subjects and measures the understanding and basic application of the topics covered.
- Cloud+, the exam includes public and private cloud, hypervisor and hardware.
- CySA+, great exam, if I have the choice I would ask my blue team to have this. I attend CySA+ SME workshops regularly to help CompTIA improve this cert.
- Pentest+, I feel this was harder than CEH or GPEN but the topics covered are the same.
- CASP, the highest certification from CompTIA, this is a good one for security architects.
- Stackable certifications, there are several career pathways, when some combination of certifications are achieved, you receive also a stackable cert, like CompTIA Secure Cloud Professional (Security+ / Cloud+), or CompTIA Security Infrastructure Expert (Security+ / CySA+ / PenTest+ / CASP) to name some.
GIAC:
- GSEC is a lot like CISSP in that is very broad but contains more technical questions and is also lengthy (5hs max). Very good for general infosec knowledge, the GSEC is a bit more technical.
- GCIH around CEH level but includes also Security Incident Handling stuff.
- GWAPT, I like it was fun, web applications are everywhere so to me this is a must have these days.
- GPEN, the exam is about penetration testing, it is a bit harder but not much than CEH.
- GCPN, the exam covers Cloud technologies and mainly AWS, Azure, Kubernetes and SAML, watch out for tricky questions.
- GXPN, the exam include really cool topics and recently incorporated a simulation as part of the written exam.
- GRID, the exam, and training are really cool about network defense with a little touch of ICS, something like 80% IT network defense and 20% ICS. You spend a lot of time playing with security onion which is really cool.
- GCFE, an excellent class, and cert, very good to understand windows internals.
- GCFA, the exam covers incident response and threat hunting, it is good but not great.
- GNFA, the exam is short and passing score is low, covers network flows and protocols, it’s a solid exam but watch out for tricky questions, double read the questions.
- GCIA, the exam about packet analysis, really cool if you like pcaps and especially helpful (to not say a must) for those pursuing the GSE.
- GCTI, is about threat intelligence, interesting and helpful for improving incident handling processes.
- GCCC, this exam covers the CIS Controls, very useful for Security Managers.
- GCPM, this is the OMG learn the PMP processes including inputs and output up and down exam.
- GSE, the mother of all GIAC certs, the multiple choice is a combo of GSEC and GCIA light with some touch of GCIH, the hands-on lab is great, you spend two full days testing the many subjects.
SANS Technology Institute (STI):
- CyberSecurity Core engineering certificate, it includes four GIAC certs, two whitepapers, netwars continuous, and the tuition fees are lower than taking the courses independently.
- Master of Science in Information Security Engineering (MSISE), it includes nine GIAC certs, two whitepapers, two presentations, netwars continuous, several other papers including two group projects, I definitively recommend it, it means a lot of work but so far it worth it and if you like SANS courses, the tuition fees are around 50% lower than taking the courses separately.
The GSE is the capstone of the MSISE, to me, it was a two day full of fun event, it is like having to play a CTF after the other, different from Netwars cyber ranges, there are no hints, the time for finishing each exercise is reduced so a good proficiency in all covered areas is required to finish on time.
As preparation for the GSE, I played Netwars Core tournament and won, played and won also the Netwars CyberDefense challenge, and did the entire CyberDefense challenge using different approaches and tools every time at home three times.
My netwars coins earned while preparing for the GSE


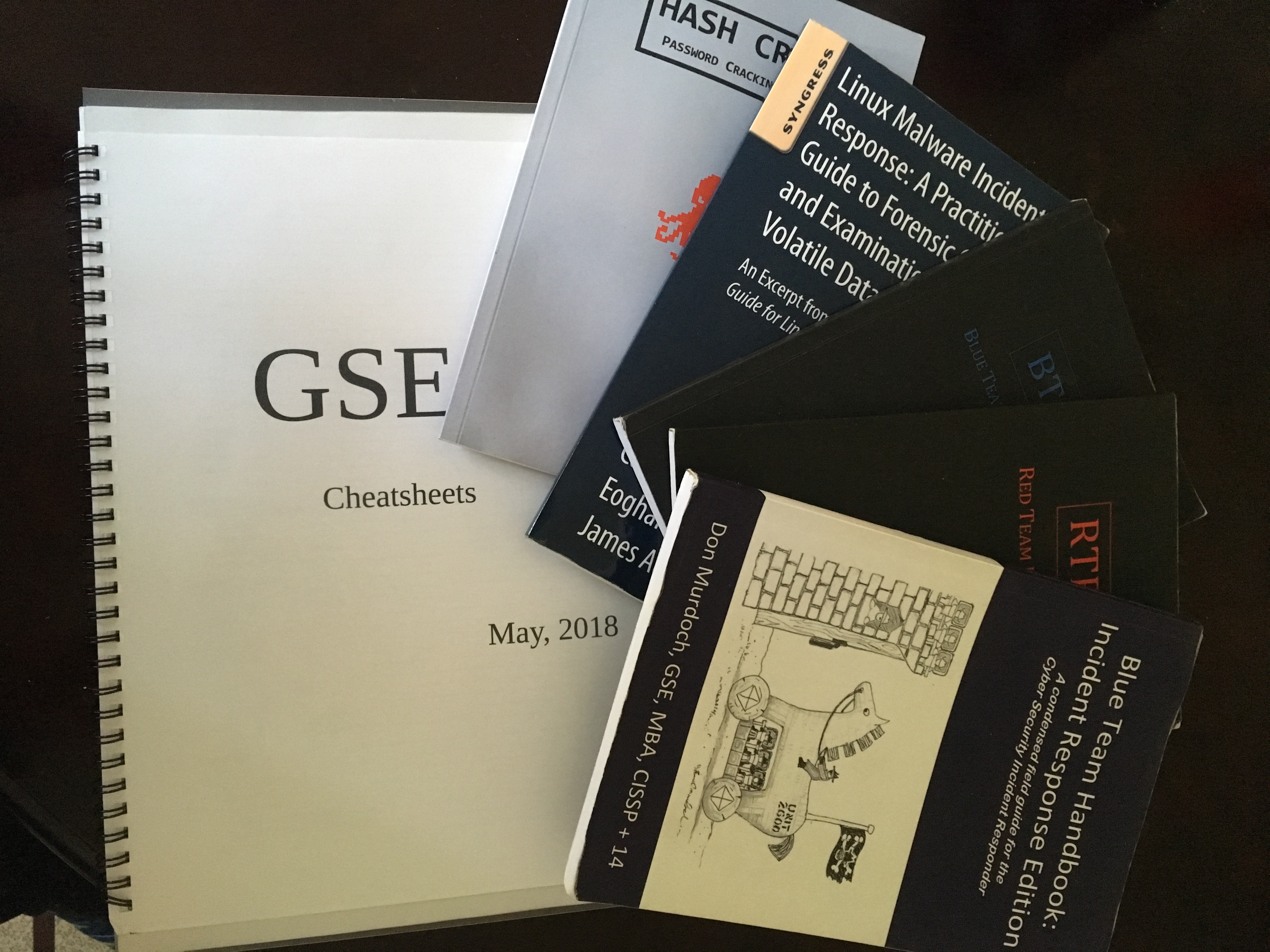
My GSE support material
Some other candidate GSE support material
Course recommendations
When asked what training and/or certifications will I recommend, often will advice to start with a generic book/training/certification like Security+ or CISSP, the cybersecurity field is huge, there are a lot of different areas of expertise, and those certifications help to get a better understanding of what every area is about. Next based on the individual preferences find something you enjoy doing.
Here are the training/books/certs I like in no particular order, some are not expensive while others (SANS) are very expensive (I did 5 SANS work-study courses to keep it on the budget, and even those are getting expensive).
Just starting:
- Read a (few) Security+ preparation guide
- Read a (few) CISSP preparation guide
- Learn Python
- SANS SEC401 GSEC bootcamp
Penetration testing:
- eLearnSecurity PTP3 eCPPTv2
- SANS SEC504 GCIH
- SANS SEC560 GPEN
- SANS SEC542 GWAPT
Follow up on penetration testing:
- Offensive Security PWK OSCP
- SANS SEC660 GXPN
Cyber Defense/Blue team:
- CompTIA CySA+
- eLearnSecurity ePWD
- SANS SEC503 GCIA
- SANS SEC511 GMON
Cloud:
- Get the Adrian Cantrill AWS trainings, they are far superior to any other material out there, check https://learn.cantrill.io/
Books:
- TCP/IP Illustrated vol 1
- WebApplication hackers handbook 2
- RTFM, Red Team Field Manual
- BTFM, Blue Team Field Manual
- Blue Team Handbook
- Practical Packet Analysis
- ModSecurity handbook (OWASP CRS is free and offers great protection)
Continuous improvement:
- Keep reading
- Keep learning
- Pick a project interesting to you in OWASP (or whenever you want) and contribute, I picked OWASP ModSecurity Core Rule Set myself
Awesome, congrats mate. Useful info.